
More and more companies are recognizing the advantages of digitization. If internal processes and workflows are digital, productivity increases and the workforce can work more flexibly. To do this, various technical components must be coordinated with one another and the employees must be trained. At the same time, the risks associated with the new technology are increasing. Technical problems, hacker attacks or application errors can lead to operational failures and harm the company.
Therefore, comprehensive and effective cloud security is an important part of protecting data.
The advantages of a cloud
Data storage in a cloud offers users several advantages:
- Fast access to the stored data from almost any end device with an Internet connection
- Increased productivity by working together on a file
- Individual adjustment of the services according to the needs of the users
- Fast and cheap implementation of new applications possible
- Regular data storage and backup of files by the provider
- Billing based on need and usage

This is how cloud security works
Cloud security includes various measures, methods, guidelines and technologies to protect data in the cloud:
- Server and network security
- Management of access rights and user credentials
- Compliance with legal requirements for data protection
- Secure access to the individual applications and the platform used
- Access to data centers only for authorized persons
The most important cloud services – an overview
In cloud computing, providers differentiate between different service models for users.
The models provide users with different ways of accessing the services.
Users do not have to buy any special hardware for this. However, companies should ensure that the chosen solution is compatible with the existing IT infrastructure.
The American National Institute for Standards and Technology (NIST) defines these four cloud services:
- IaaS: Infrastructure as a Service
- PaaS: Platform as a Service
- SaaS: Software as a Service
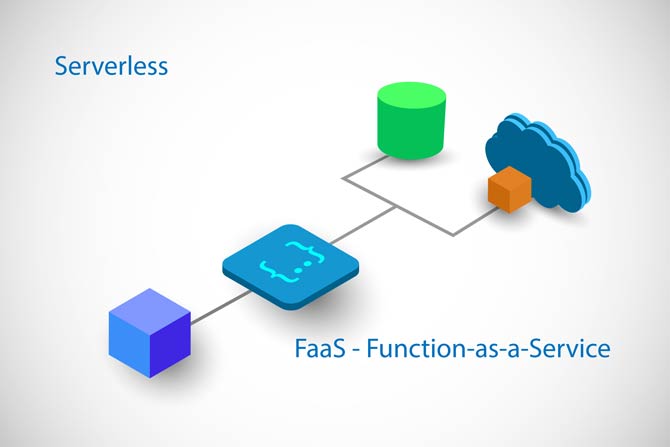
- FaaS: Function as a Service
IaaS: Infrastructure as a Service
IaaS is a cloud service that provides the hardware and resources for users. This includes data storage, network technology and servers. With IaaS, users do not have to operate their own data center.
The provider also takes care of the maintenance and updating of the individual components. The resources can be adjusted as needed. Users only pay for the applications they use.

PaaS: Platform as a Service
With PaaS, a third party provides the necessary hardware and a platform for the application software.
It is primarily a solution for companies that develop their own application programs.
The programmers do not have to set up their own IT infrastructure for this. Instead, they can use PaaS to develop, manage, and run their own applications.
SaaS: Software as a Service
With SaaS, an external provider operates both the software and the IT infrastructure. Users can access the provider’s platform via an Internet browser. The users rent the applications and use them as services.
The provider issues licenses and offers subscriptions for which users pay fees. In order for SaaS to run smoothly, subscribers should have a fast and stable Internet connection, which they must take care of themselves.
FaaS: Function as a Service
FaaS can be assigned to so-called serverless computing, i.e. applications that are created and run without their own server administration. Users only pay a fee to the provider when the applications they develop are executed via code.
Cloud environments – you should know that
In addition to cloud services, the National Institute for Standards and Technology (NIST) also defines four cloud environments on which the data is delivered:
- Public Cloud: This model can be shared by many users over the Internet. Users can use storage space, computing power and various applications for a fee without investing in the appropriate hardware or software themselves.
- Private Cloud: With the private cloud, the provider assigns cloud computing to just one user. This can be a specific company or an organization.
- Hybrid Cloud: The hybrid cloud is a combination of a private cloud and a public cloud. Companies often use the hybrid cloud for short-term projects to save costs.
- Community Cloud: The community cloud is used by companies together with several partners. These are customers, business partners and employees. Communication between those involved and working together on projects is facilitated via the community cloud.
More security with cloud security
Cloud security warns unauthorized users, detects weaknesses in the system at an early stage, detects and eliminates security-related events, and implements corrective measures to limit damage.
These measures ensure optimal security with cloud security:
- Data security through data encryption and secure data transfer through virtual private networks (VPN).
- Identity and access management (IAM) through secure passwords and multi-factor authentication of users.
- Secure data storage in the cloud with regularly updated security solutions from the provider.
- Securing the interfaces between users, software and network. Bechtle Cloud Security defines the surface to be protected for your company, records the various access paths and designs, maintains and monitors a secure network.
Source: https://www.blog.de/schutz-fuer-daten-cloud-security/


