Scientists have developed a stretchable jelly battery inspired by electric eels. The technology could...
Chinese researchers have produced environmentally friendly batteries from recycled solar panels. This could not...
Oksana Lukyanenko has been General Manager for Germany at Wolt since mid-2022. Wolt “We...
Reddit has apparently blocked numerous search engines to prevent them from displaying content from...
A simple job where you can earn a lot of money quickly and easily?...
The two Bunch founders Enrico Ohnemüller and Levent Altunel.Bunch Two years after the seed...
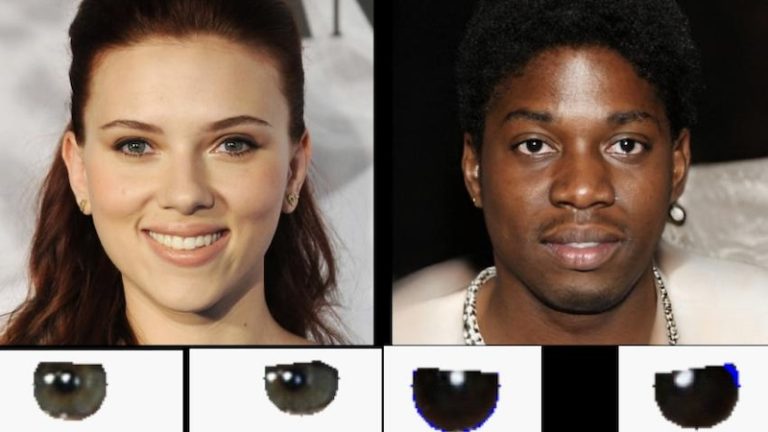
More and more deepfakes are circulating on the Internet. They pose a danger because...
While some people see artificial intelligence as a threat to their jobs, it also...
If the display on an electricity meter fails, it is usually no longer usable....
CONET will also have a stand at this year's LogiMAT, the international trade fair...